Identity as a Service
One platform. All identities.
The world is going digital. More apps, more decentralization, more remote & home office - nevertheless, secure access to corporate resources must be guaranteed. However, the manual, error-prone management of user identities and authorizations comes with great risks: data breaches, financial losses, image damage. That‘s why the EU GDPR requires the consolidation of access rights, a clear authorization concept and corresponding proof of compliance.
- Do you want to protect yourself better with access management & multi-factor authentication?
- Do you want to minimize the uncontrolled growth of applications, authorizations, access management & their administration?
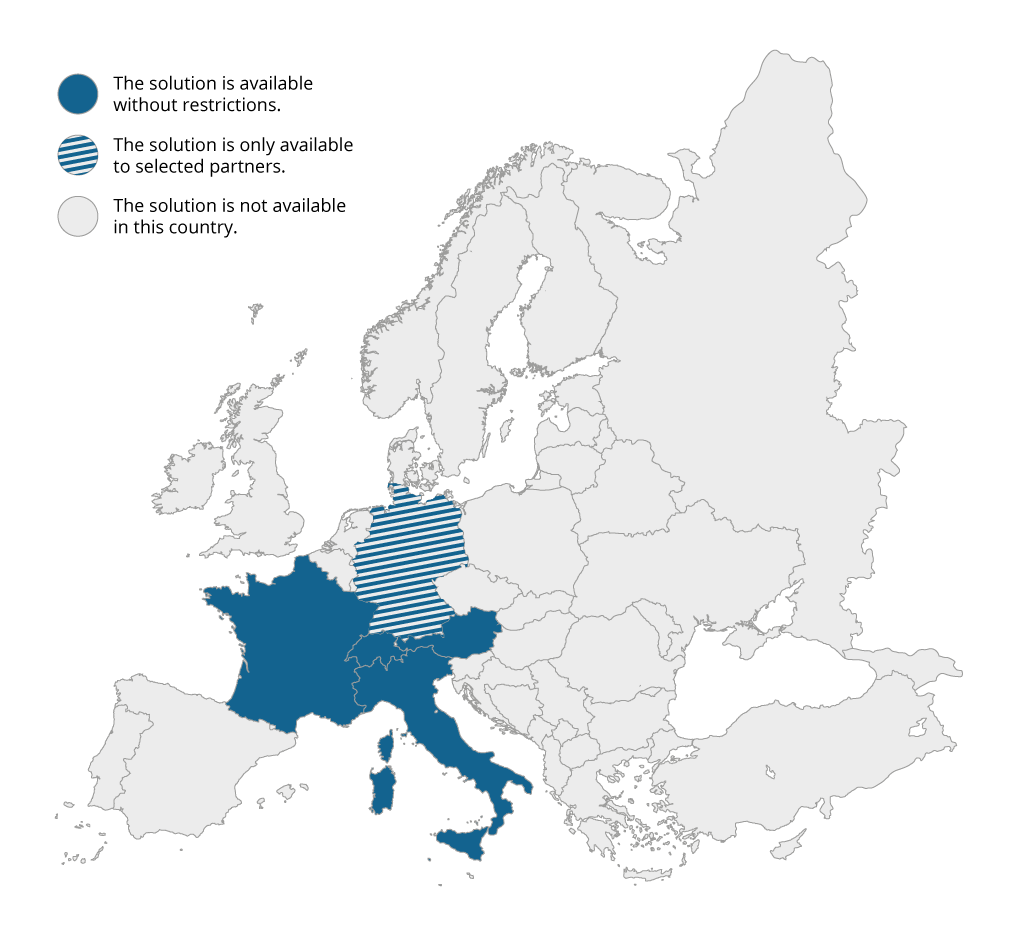
- Do you want to meet legal requirements without outsourcing sensitive data & identities to the USA?
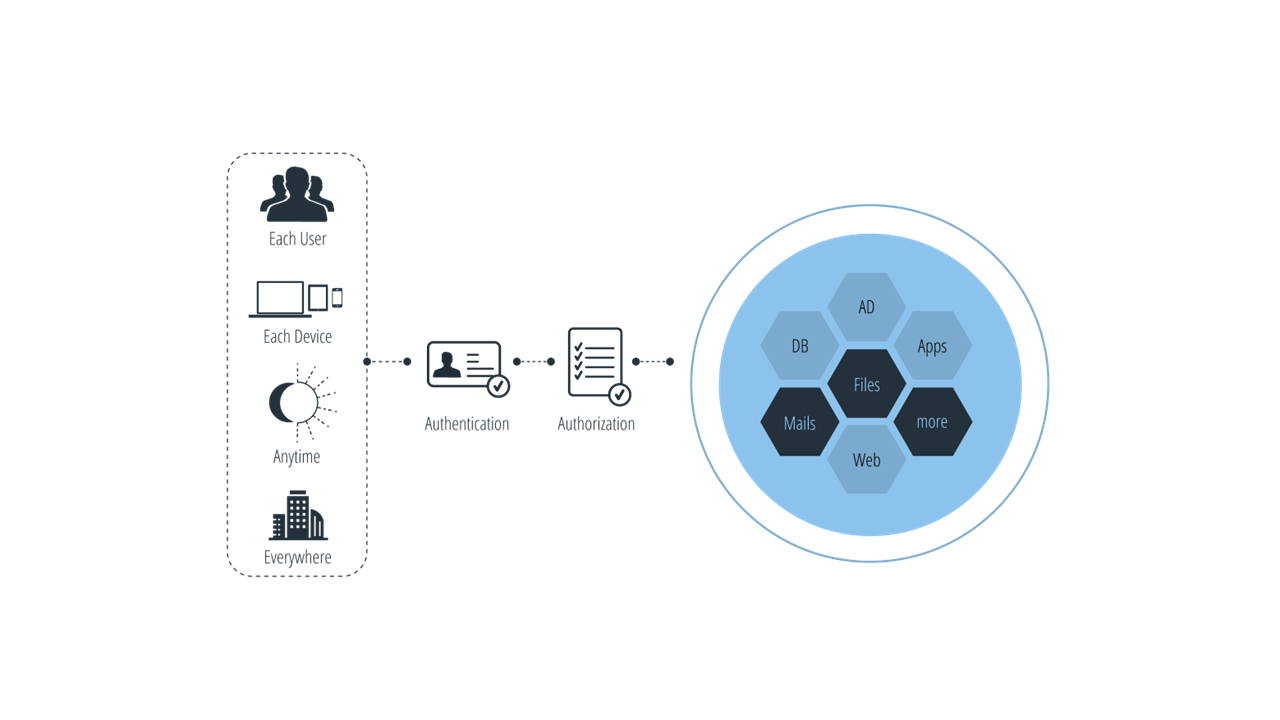
With DTS Identity, we ensure that only authorized persons are granted access to predefined apps and data and are given exactly the right rights at the right time. Our (customer) identity & access management (IAM & CIAM) automates the management of digital identities and enables identification, authentication and authorization - essential foundations of a zero trust strategy!
As an IT security software vendor, we have developed the platform to decouple IAM & CIAM from individual apps and manage them centrally. The result is a single, secure portal for users and apps - for entire companies, their connections and customers. „Security Software by DTS“ combines a central, intuitive, midmarket-friendly IAM & CIAM with access control as well as rights and profile management - scalable from the German, certified DTS Cloud!
The service
DTS Identity in detail
WE MAKE LIFE EASY FOR YOU!
In many companies, there are countless apps or micro services that different user groups can access on a daily basis. The number of apps is growing exponentially. An overview and thus control is lost. With DTS Identity, all apps can be bundled with an OIDC or SAML login standard and are visible at a glance. Via single sign-on (SSO), each user can log in for their respective local or cloud apps via multi-factor authentication. This means that you or your customers log in centrally only once, see all apps released for them and have direct access. A separate database manages the data. In addition, existing directories can be used for authentication, group management and storage of attributes via an AD/LDAP connection.
DTS Identity can be provided for employees, customers and partners. The central identity management for B2B, B2C and B2E shows all integrated apps at a glance. With just a few clicks, it is possible to configure for whom and which apps the desired access policies apply. With the help of role-based access control (RBAC), it is also possible to assign different roles. As soon as a user is assigned a role, he or she receives the predefined rights.
The intuitive dashboard enables simple management. Each user can edit their data, settings and authentication factors on the self-service interface. Admins see all activity in the platform and can configure connected organizations, apps, APIs, users, permissions and roles.
LESS CHALLENGES, MORE CORE BUSINESS
The manual managing of user accounts, access rights and backing up sensitive data is time-consuming and error-prone. We minimize your effort and save valuable time through automated rights management, cross-location onboarding and offboarding, and „by the way“ a concrete authorization concept is created. In addition, you save money. On average, about 1/3 of the IT budget is spent on licenses. Now you can allocate expensive licenses only to those only to those users who actually need them.
CIAM – THE CUSTOMER EXPERIENCE MATTERS!
Digital transformation is also changing the way you interact with your customers. Customer expectations of user experience are high, especially in terms of ease of access, while at the same time security. If companies fail to deliver on this, customers will switch to the competition. Customer identity & access management is fundamental to the customer journey.
DTS Identity can be embedded in customer applications and online services for customers. A transparent and secure user experience is ensured at every stage of the customer lifecycle. In acquisition and customer retention, DTS Identity helps with easy registration, SSO and fast onboarding. For subsequent strong customer loyalty, the platform supports personalized customer experiences through dynamic profile extensibility. For solidified customer trust, customers can transparently view their profiles and add or update them as appropriate - all while complying with all data protection regulations, of course.
WE SEE. WE DO. SAFE!
Identity theft and fraud is one of the biggest cyber threats. Especially if there is no IAM & CIAM, the vulnerability is huge, especially because the compromised users usually have many accesses and access rights. As an IT security software vendor, it is part of our self-image to prevent this. On the one hand, by enforcing the principle of least privilege. On the other hand, through numerous security features. For example, passwords for external systems are already encrypted in the browser and never accessed via DTS Identity. As protection against brute force attacks, the software compares the most common passwords with the user‘s selection and prompts the user to use a different one if necessary. If compromised login credentials are used, breached password detection enables identification of the user and password and provides direct response options.
IDENTIFY!
DTS Identity is exactly one platform for all identities and enables IAM & CIAM at the highest level. It ensures that only authorized and legitimate identities access IT resources. It enables easy authentication and centralized profile as well as rights management. It protects sensitive data, increases your security level and forms the basis for meeting compliance requirements and internal guidelines. It increases productivity and efficiency. It provides a great user experience and customer journey and reduces the burden on you and your IT team. We provide the DTS Identity with all features in a single license, from our DTS Cloud, incl. 24/7 support - easy to use & easy to pay!
Only 14% of all users use VPNs to protect their identity, even though this contributes much more safety. Matching to this: Check out our additional flyer on secure remote access with DTS Identity!
DTS Identity for secure remote access
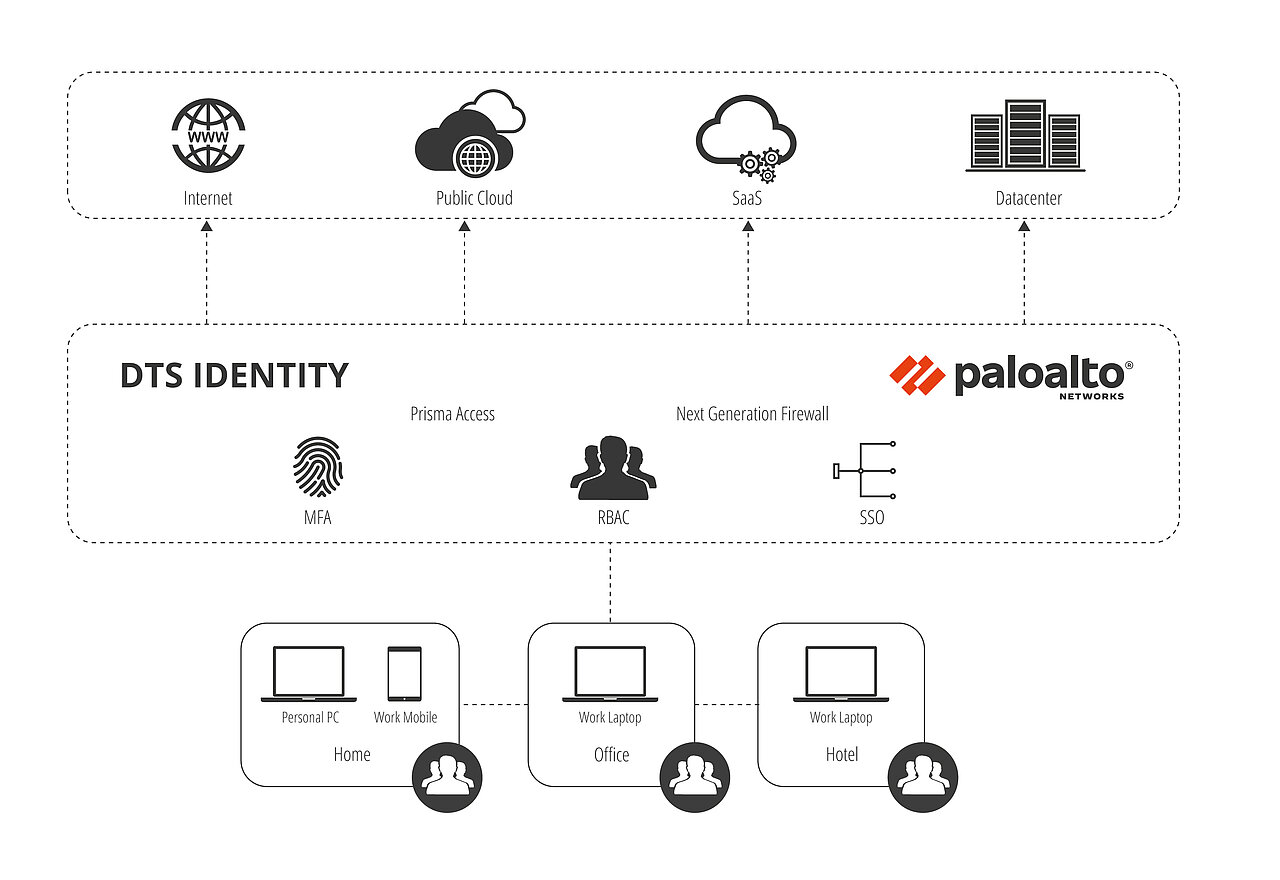
DTS Identity & Palo Alto Networks
GENERAL CHALLENGE
Enterprises face ever-increasing security challenges as more users, data, and services operate outside traditional network boundaries. Employees use numerous on-premises and SaaS applications to get their work done. Often, organizations use different, separate products to address the security needs of remote workers. This approach has led not only to higher management costs and increased complexity, but also to an inconsistent user experience.
SOLUTION: DTS IDENTITY & PALO ALTO NETWORKS
DTS Identity and Palo Alto Networks enable fast and secure implementation of remote employee policies. Integrating DTS Identity with Palo Alto Networks security capabilities provides secure remote access that minimizes the risk of successful cyberattacks while reducing cost and complexity. Regardless of your location or the applications you use, users securely access the applications they need without compromising the user experience. Palo Alto Networks' Prisma Access, as well as DTS Identity, are cloud-native, enabling rapid deployment and high scalability. It also reduces the need for on-premises hardware and the operational burden on network and security teams.
Enterprises with next-gen hardware firewalls can also take advantage of the collaboration through integration with GlobalProtect agents.
USE CASE 1: MORE SAFETY THROUGH MFA
In many environments, multi-factor authentication (MFA) is required to increase security when accessing critical systems or to meet compliance requirements. However, integrating MFA into existing login processes is often both complex and time-consuming. This complicates implementation and causes delays.
SOLUTION:
DTS Identity offers multiple MFA authentication options and integrates seamlessly with Prisma Access to enable customers to quickly set up MFA policies without taking critical resources offline. With Prisma Access, you can choose to enforce MFA for specific users, applications, or all without having to modify existing applications to meet security requirements.
USE CASE 2: SMOOTH USER ACCESS
Traditional VPN solutions often use the infrastructure in the customer's data center. Often, all user traffic is routed through before it reaches the Internet or SaaS applications. This routing can lead to performance degradation and bottlenecks that impact the user experience. In the process, a poor user experience can lead to a major security risk for devices and data integrity as users attempt to bypass security mechanisms, such as VPN, or use personal credentials for SaaS applications.
SOLUTION:
With DTS Identity and Palo Alto Networks, your remote workers enjoy a straightforward, easy-to-use, secure connection whether they're accessing the web, SaaS, or public, hybrid, or private clouds. Palo Alto VPN client GlobalProtect provides always-on connectivity across a range of operating systems and devices, eliminating the need to launch a VPN or log in to a web gateway.
DTS Identity's SSO integrates with Prisma Access to ensure users only need to enter a single set of credentials instead of remembering multiple passwords and authentication schemes for different applications.
While employees can seamlessly access the applications they need, role based access with DTS Identity enables a centralized location for administrators to grant access only to the resources a particular user needs.
INTEGRATION ADVANTAGES
Business agility: This cloud-native, integrated solution gives organizations the flexibility to adapt to individual needs. It is quick to implement and scalable, making it easy to adapt to changes in the business landscape.
INCREASED SECURITY
The solution reduces the risk of cyberattacks and potential security-related incidents that could damage the company's reputation. This helps to strengthen the security posture and protect sensitive corporate data.
COST AND COMPLEXITY REDUCTION
The integration of security functions unites separate security products, which means that they are no longer needed. This in turn leads to cost savings and a reduction in complexity.
INCREASE USER PRODUCTIVITY
The solution increases user satisfaction and efficiency by ensuring a consistent, fast and secure user experience from any location, regardless of the devices used and for all applications.







 isl.de
isl.de